CPU Experiment Pack
Description
This Gremlin CPU Experiment Pack shares how you can utilise the Gremlin CPU attack. CPU Attacks are available with your Gremlin account.
What’s Included
- Ability to run a CPU attack on cloud infrastructure hosts & containers on AWS, Azure, GCP & more
- Ability to run a CPU attack on cpu containers running locally with Docker
What we’ll break
With Gremlin, you have the ability to cpu attack any host or container wherever it may reside.
This pack includes 4 x 5 minute experiments:
- Experiment 1: CPU Attack a cloud infrastructure host using Gremlin
- Experiment 2: CPU Attack a cloud infrastructure Docker container using Gremlin
- Experiment 3: CPU Attack a Kubernetes pod using Gremlin
- Experiment 4: CPU Attack a local Docker container using Gremlin
- Experiment 5: CPU Attack a cloud infrastructure host using the Gremlin API
What you’ll need
- A Gremlin account (sign up here)
- Your Gremlin daemon credentials
- Cloud Infrastructure hosts (e.g. an AWS EC2 instance)
- Cloud Infrastructure containers (e.g. A DigitalOcean Docker Droplet)
- A Kubernetes cluster with access to run a daemonset (e.g. Azure AKS)
- Docker running locally (e.g. Docker for Mac)
Get ready to unleash chaos, get your credentials!
After you have created your Gremlin account (sign up here) you will need to get your Gremlin daemon credentials.
Login to the Gremlin App using your Company name and sign-on credentials. These details were emailed to you when you signed up to start using Gremlin.
Get a free Datadog trial to monitor your chaos 💥
Learn how to implement Chaos Engineering with Gremlin and Datadog.
Get your free 1 week Datadog trial account here: https://www.datadoghq.com/partner/gremlin-chaos-monitoring/.
Install your Datadog agent on each of your hosts or as a container by following the Datadog agent installation guide available within the Datadog App.
Experiment 1: CPU Attack a cloud infrastructure host using Gremlin
Step 1.0 - Installing the Gremlin Daemon and CLI
First, ssh into your server and add the Gremlin Debian repository:
Import the repo’s GPG key:
Then install the Gremlin agent:
Step 1.1 - Configuring the Gremlin Agent
After installing the agent, you'll need to authenticate it with the Gremlin Control Plane.
Start by initializing Gremlin and assigning tags with the following command. Substitute your desired tag name for <span class="code-class-custom">service=api</span>:
Now you’re ready to run attacks using the Gremlin.
Step 1.2 - Run a CPU Attack Using Gremlin
Using your Gremlin login credentials (which were emailed to you when you created your account), log in to the Gremlin App. Then click Create Attack.
First choose your target by selecting the host you registered with Gremlin:

Next we will use the Gremlin App to create a CPU Attack. Choose the Resource Category and Select the CPU Attack:
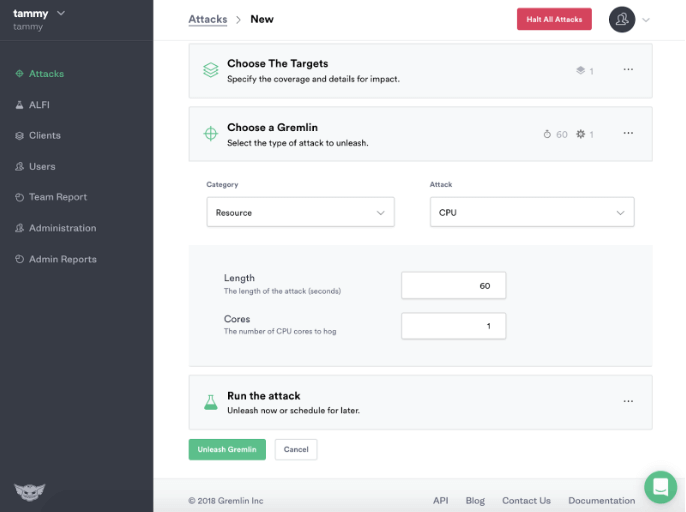
Click Unleash Gremlin and the Gremlin CPU Attack will consume CPU resources on your host.
You can now view the Gremlin CPU Attack in Datadog:

Experiment 2 - CPU a cloud infrastructure container using Gremlin
Step 2.0 - Install Docker
In this step, you’ll install Docker.
Add Docker’s official GPG key:
Use the following command to set up the stable repository.
Update the apt package index:
Make sure you are about to install from the Docker repo instead of the default Ubuntu 16.04 repo:
Install the latest version of Docker CE:
Docker should now be installed, the daemon started, and the process enabled to start on boot. Check that it’s running:
Make sure you are in the Docker usergroup, replace $USER with your username:
Log out and back in for your permissions to take effect, or type the following:
Step 2.1 - Create an htop container for monitoring
Htop is an interactive process viewer for UNIX. We’ll use it to monitor the progress of our attacks.
First create the Dockerfile for your htop container:
Add the following to the Dockerfile:
Build the Dockerfile and tag the image:
Run htop inside a container, this will monitor the host:
To exit htop, enter q.
Next we will create an NGINX container and monitor it directly by joining the container’s pid namespace.
Step 2.2 - Create an NGINX container to attack
First we will create a directory for the html page we will serve using nginx:
Create a simple HTML page:
Paste in this content:
Create a container using the nginx Docker image:
Make sure the docker-nginx container is running:
Step 2.3 - Set up your Gremlin agent credentials
The Gremlin daemon (<span class="code-class-custom">gremlind</span>) connects to the Gremlin backend and waits for attack orders from you. When it receives attack orders, it uses the CLI (<span class="code-class-custom">gremlin</span>) to run the attack.
Step 2.4 - Run the Gremlin Daemon in a Container
Use docker run to pull the official Gremlin Docker image and run the Gremlin daemon:
Use docker ps to see all running Docker containers:
Jump into your Gremlin container with an interactive shell (replace 7167cacb2536 with the real ID of your Gremlin container):
From within the container, check out the available attack types:
Then exit the container.
Step 2.5 - Run a CPU Attack against the NGINX container from a Gremlin Container
In this step we will run gremlin attack-container to target the NGINX container by its ID and run a CPU Attack against it.
Before running the CPU attack, use htop to monitor the docker-nginx container (replace f291a040a6aa with your docker-nginx container ID):
Run the following to create the CPU container attack against the container (replace f291a040a6aa with your docker-nginx container ID):
Now use your htop container to monitor the results:
You will also see Gremlin consuming CPU resources in Datadog:

Experiment 3 - CPU a Kubernetes pod using Gremlin
Kubernetes is a container management system which is built with reliability in mind. Architecture is commonly 1 master and 2 or more nodes which are replicated from the master. When the master dies the nodes are ready to replace it. When one node dies another will be ready to replace it.
Step 3.0 - Retrieve Your Team ID and Secret Key
To install the Gremlin agent and Kubernetes agent, you will need your Gremlin Team ID and Secret Key. If you don’t know what your Team ID and Secret Key are, you can get them from the Gremlin web app.
Visit the Teams page in Gremlin, and then click on your team’s name in the list.
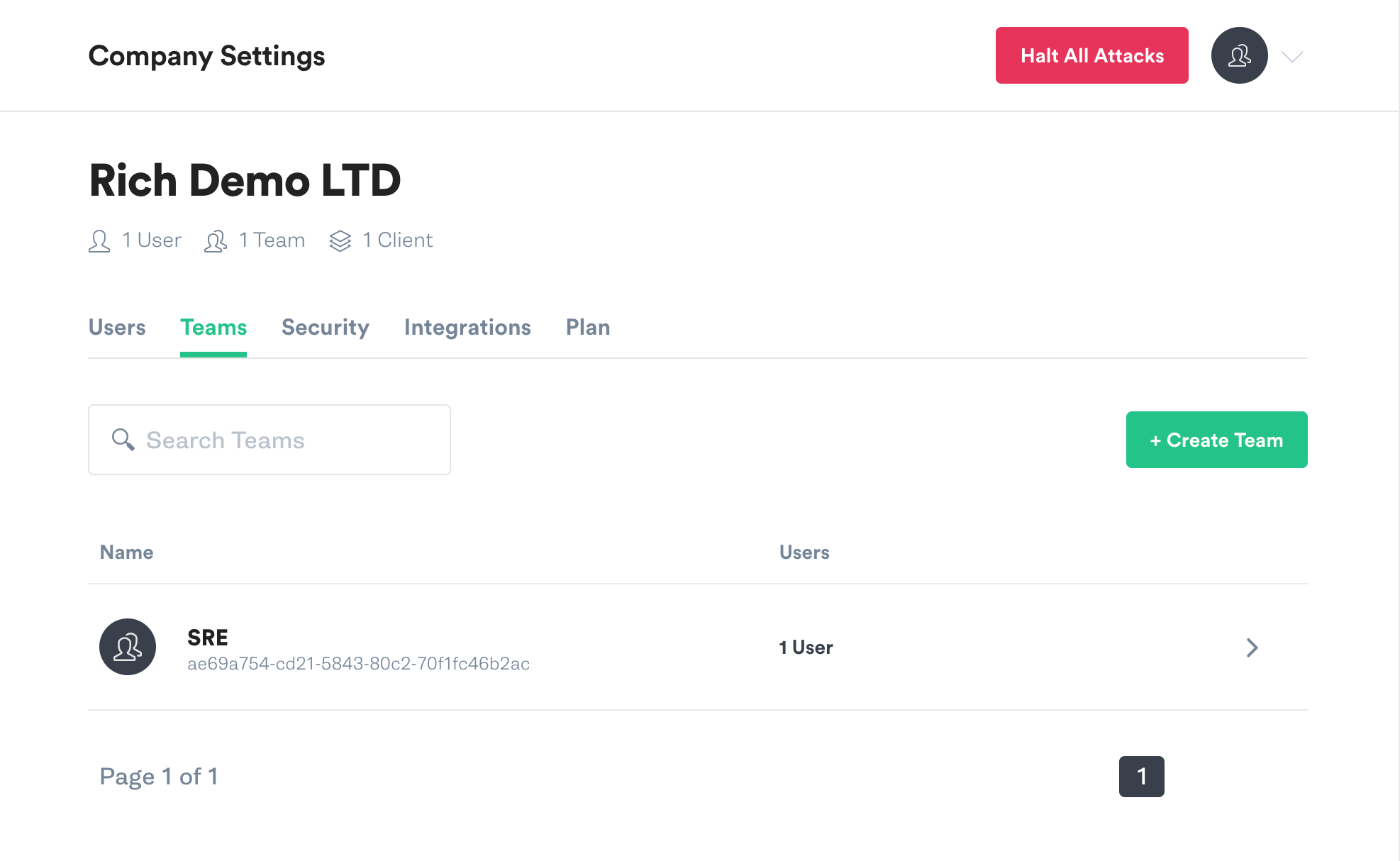
On the Teams screen click on Configuration.
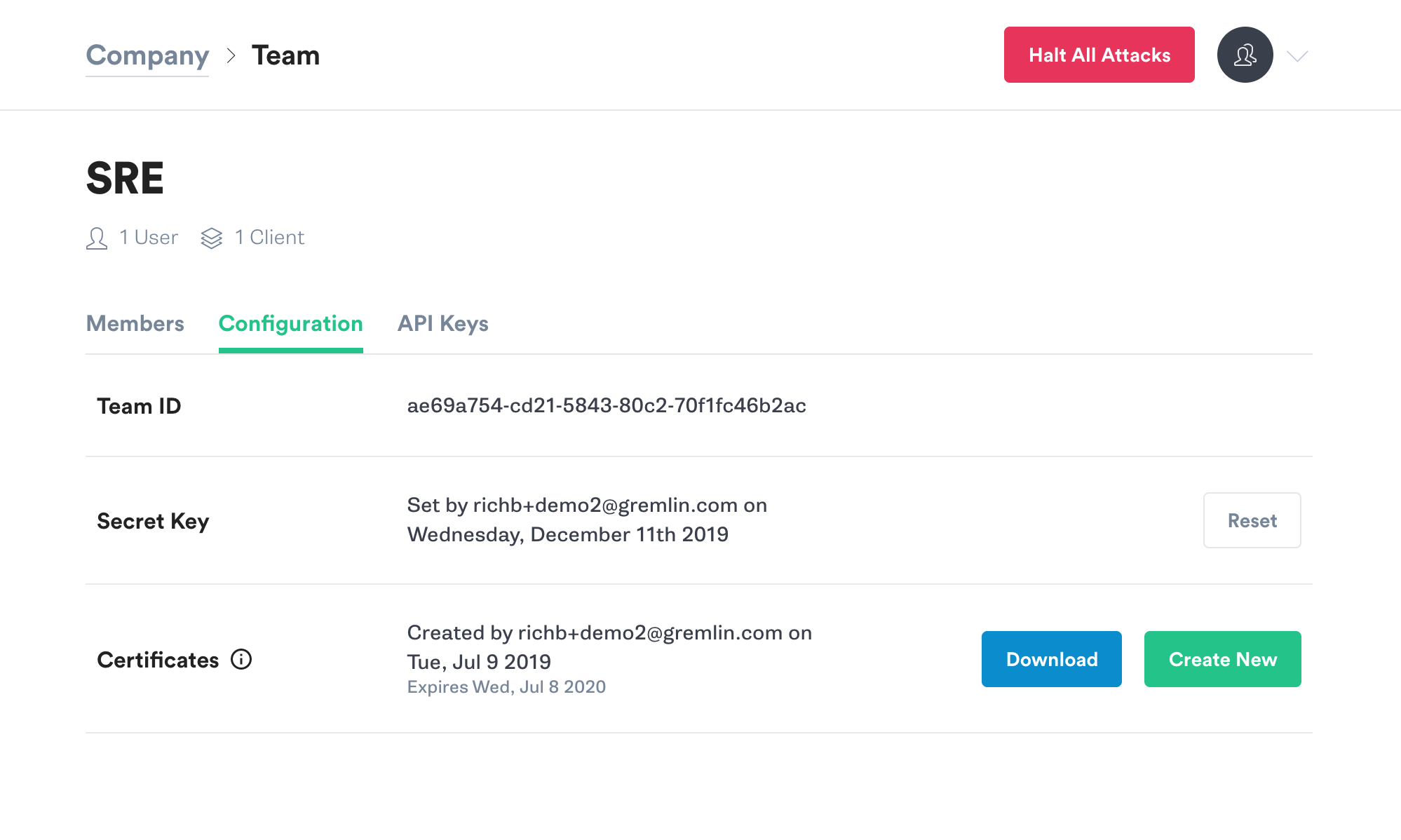
Make a note of your Team ID.
If you don’t know your Secret Key, you will need to reset it. Click the Reset button. You’ll get a popup reminding you that any running agents using the current Secret Key will need to be configured with the new key. Hit Continue.
Next you’ll see a popup screen that will show you the new Secret Key. Make a note of it.

Step 3.1 - Install Gremlin with Helm
The simplest way to install the Gremlin agent on your Kubernetes cluster is to use Helm. If you do not already have Helm installed, go here to get started. Once Helm is installed and configured, the next steps are to add the Gremlin repo and install the agent.
Add the Gremlin Helm chart:
Create a namespace for the Gremlin Kubernetes agent:
Next you will run the <span class="code-class-custom">helm</soan> command to install the Gremlin agent. In this command there are three placeholder variables that you will need to replace with real data. Replace <span class="code-class-custom">$GREMLIN_TEAM_ID</span> with your Team ID from step1, and replace <span class="code-class-custom">$GREMLIN_TEAM_SECRET</span> with your Secret Key from step 1. Replace <span class="code-class-custom">$GREMLIN_CLUSTER_ID</span> with a name for the cluster.
If you are using Helm v3, run this command:
For older versions of Helm, use the --name option:
If you’re not sure which version of Helm you’re using, run this command:
For more information on the Gremlin Helm chart, including more configuration options, check out the chart on Github.
Step 3.2 - Creating attacks using the Gremlin App
Example: Creating a CPU Attack against a Kubernetes node using the Gremlin App
You can use the Gremlin App or the Gremlin API to trigger Gremlin attacks. You can view the available range of Gremlin Attacks in Gremlin Help.
The “Hello World” of Chaos Engineering is the CPU Resource Attack. To create a CPU Resource Attack, click Attacks in the left navigation bar and New Attack.
Host targeting should be selected by default. Click on the Exact button to expand the list of available hosts, and select one of them. You’ll see the Blast Radius for the attack is limited to 1 host.
Click on “Choose a Gremlin” and select “Resource” and then “CPU.”
The CPU Resource Attack will consume CPU resources based on the settings you select. The most popular default settings for a CPU Resource Attack are pre-selected, a default attack will utilize 1 core for 60 seconds.
When your attack is finished it will move to Completed Attacks in the Gremlin App. To view the logs of the Attack, click on the Attack in Completed Attacks then click to the arrow to view the logs.
Experiment 4 - CPU a local Docker container using Gremlin
Step 4.0 - Install Docker For Mac
First you will need to install Docker For Mac if you do not yet have it on your local computer, follow the instructions provided by Docker.
Step 4.1 - Set up your Gremlin credentials
The Gremlin daemon (gremlind) connects to the Gremlin backend and waits for attack orders from you. When it receives attack orders, it uses the CLI (gremlin) to run the attack.
Step 4.2 - Create a Gremlin Docker container
Use docker pull to pull the official Gremlin Docker image:
Step 4.3 - Create an NGINX container to attack
First we will create a directory for the html page we will serve using nginx:
Create a simple HTML page:
Paste in this content:
Create a container using the nginx Docker image:
Make sure the docker-nginx container is running:
Step 4.4 - Run A Gremlin CPU Attack
Now use the Gremlin CLI (gremlin) to run a CPU attack from within a Gremlin container:
This attack will run a CPU attack on your Nginx container.
Experiment 5: CPU Attack on a cloud infrastructure host using the Gremlin API
It is also possible to run attacks programmatically using the Gremlin API. We will run these attacks from a Mac OS laptop.
Step 5.0 - Installing the Gremlin Daemon and CLI
First, ssh into your server and add the Gremlin Debian repository:
Import the repo’s GPG key:
Then install the Gremlin daemon and CLI:
Step 5.1 - Register your server to the Gremlin control plane
Using your Gremlin login credentials (which were emailed to you when you created your account), log in to the Gremlin App. Open Settings and copy your Team ID and Secret.
Initialise Gremlin by running the following command and follow the prompts to enter your Gremlin Team ID and Secret:
Now you’re ready to obtain your Gremlin API token.
Step 5.2 - Obtain your Gremlin API token
First access your Gremlin API token by providing your gremlin username and password to /users/auth, replacing your email, password and company name in the curl request below:
Your API token will be displayed on the screen. The example below shows "Bearer Y4MGE3MGMzOmdyZW1saW5AZ3JlbWxpbmluYy5jb206NWNhMWFiMWU" as the API token that will be used for interacting with the Gremlin API:
Step 5.3 - Store your Gremlin API token
On your local computer (Mac OS), store your Gremlin API token as an environment variable:
Check to ensure you have set your token correctly:
Your API token will be displayed on your terminal screen:
Now you’re ready to run attacks using the Gremlin API .
Step 5.4 - Run a CPU Attack Using The Gremlin API
Now you’re ready to run a shutdown attack using the Gremlin API . Run the following command on your local computer (Mac OS):
View the attack in progress using the Gremlin API:
Your current attack will be displayed in terminal:
Avoid downtime. Use Gremlin to turn failure into resilience.
Gremlin empowers you to proactively root out failure before it causes downtime. See how you can harness chaos to build resilient systems by requesting a demo of Gremlin.

.svg)

.svg)
.svg)

 This is an older tutorial
This is an older tutorial